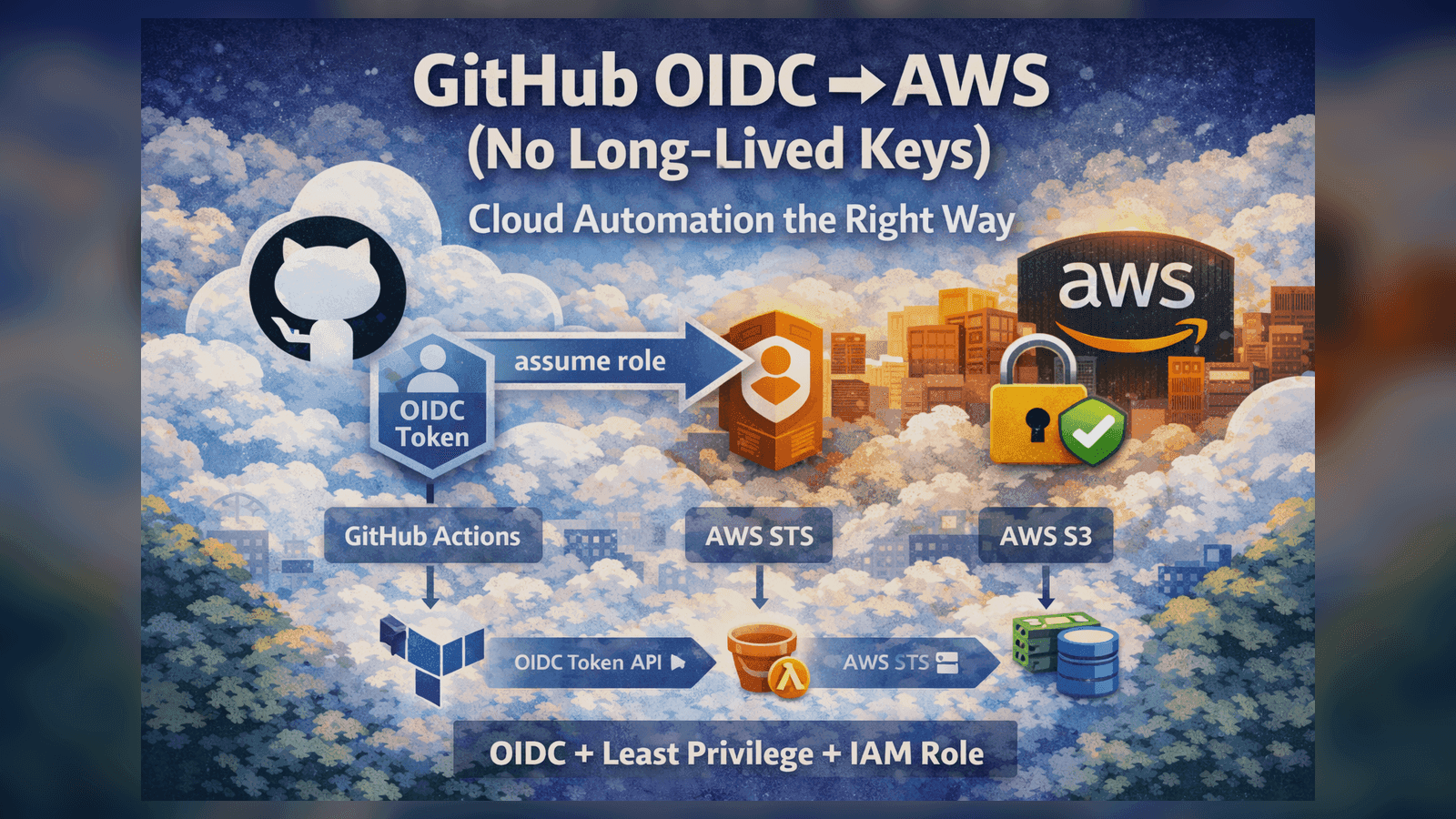
GitHub OIDC → AWS (No Long-Lived Keys): Cloud Automation the Right Way
How to use GitHub Actions OIDC to assume an AWS IAM role and deploy/upload artifacts without storing AWS keys. Includes least-privilege IAM, trust policy patterns, and troubleshooting tips.
GitHub OIDC → AWS (No Long-Lived Keys): Cloud Automation the Right Way
Static AWS keys in CI are a footgun.
If you want cloud automation that scales (and passes security review), use OIDC-based federation:
- GitHub Actions issues a short-lived identity token (OIDC)
- AWS STS exchanges it for short-lived AWS credentials
- Your workflow assumes a least-privilege role and does the work
This portfolio uses the same pattern to support Cloud telemetry mode (AWS S3) without ever embedding long-lived credentials.
The architecture
GitHub Actions → OIDC token → AWS STS AssumeRoleWithWebIdentity → IAM Role → S3 write
Why this matters
- No credential rotation
- Blast radius is smaller (short-lived creds)
- Easy to lock down by repo/branch/environment
What I shipped in this portfolio
- Terraform module that provisions S3 + IAM role with an OIDC trust policy
- A GitHub workflow that uploads a metrics artifact to S3
- A dashboard mode that reads from S3 (with safe fallback)
Takeaway
If you’re building cloud automation, treat identity as part of the system design. OIDC + least privilege is the modern baseline.
Tagged with:
Found this helpful?
I'm available for consulting and full-time QA automation roles. Let's build quality together.